Pete Flecha and I co-host the Virtually Speaking Podcast. We both get emails, calls, and texts from various people wanting to start a tech podcast. I figured I’d sort some of the most common advice into a single blog with maybe some follow up blogs for more in-depth gear reviews etc. Note There are some strong opinions I hold here loosely and I look forward to the twitter banter that will follow.
Who
Because AI machine learning hasn’t figured out how to podcast yet, you are going to need to sort out who will come on the podcast.
Will you have a single host, a pair of hosts, a panel?
First, how many hosts you have is going to be partly a function of how long the podcast runs for. It’s hard to have a 6-minute podcast with a 5 person panel. Inversely the more people involved in a podcast, the more hell you face trying to align the Gantt chart that is everyone’s schedule and time zone requirements.
The vSpeaking Method for hosts? We generally stick to 2 host. We leverage a guest host filling in when one of us is traveling, or in a conference session and 2 guests. Another benefit of the occasional guest host is they can help interview on a topic that presenters are still getting up to speed on. An example of this is when we tagged in Myles to help with discussing containers and other devops hipster things with Chad Sakac.
What makes a good host?
This is going to be a bit of a philosophical discussion as a lot of things can make for a good host but some general thoughts on traits that help with sucucess:
- Someone needs to push the show forward, keep it on task and time and be a good showrunner.
- Someone needs to know enough about the topic to discuss it, or ask the guests about it. Someone who’s willing to do the research on the product and field more than 5 minutes beforehand.
- Someone skilled and willing to do the editing.
- Someone who can handle publicizing the podcast. (The vSpeaking Podcast doesn’t pay for promoted tweets or google AdWords).
- People (if plural hosts) who are good at reading a conversation and knowing when to jump in and out.
- Flexible schedules. I’ve recorded at all kinds of weird hours to try to support overseas guests, recording at weird hours while we were traveling to get US guests. Remember, The world does not revolve around the Pacific time zone.
Inversely there are some behaviors or environmental variables for hosts that may inhibit success.
Some traits can be problematic in hosts:
- People who lack commitment or “air cover from management” to stay committed beyond a few episodes. If your manager is going to be asking “what is the value in this” it may be problematic to maintain this as a work hours activity.
- A host who likes to hear the sound of their own voice. Remember it’s a podcast, not a monologue.
- A host who thinks they know more about the subject than they do. this will manifest itself in awkward questions, disagreements and the host talking too damn much.
- Hosts with zero understanding of the technology. If it’s just a product marketing intern reading a FAQ, no one will listen to it (if you are lucky!)
Will there be guests on every episode?
Having a constantly rotating cast of guests provides a lot of benefits as it helps open up the topics and information you bring in.
there is a class of podcasts that tends to diverge from this. The ‘news of the week’ format. A solid example of this would be something like the Six Five. I’ll caution there are a LOT of podcasts who fall into this camp and even executed well it has some challenges. This may sound easier in that you do not have to do any scheduling of guests, but done properly it is more time-consuming format as it requires you to be the subject matter expert on everything. This is best executed in niche fields (rather than the entire tech industry), and best executed by seasoned veterans who can provide more than the surface commentary and repeating what TheRegister wrote for commentary. Expect to do twice as much research when you have to be able to understand both the question AND the answer.
What
What topics will you cover?
This can be a difficult one. Creating a 100 episodes on JUST Microsoft Exchange would be difficult, exhausting, and likely result in most people (even people who are full time exchange admins) losing interest. There are ways to accomplish your goal of promoting a given product without making it front and center the focus of EVERY single episode. Find common adjacent products, products that integrate, fundamental technologies that every admin using said product needs to know.
The vSpeaking Podcast method: While I wouldn’t mix in an episode on woodworking we’ve found some back to the basics, Topical episodes, and partner episodes help keep things fresh. A major commitment we made from the beginning was to have the majority of our content be “evergreen”. The goal being that if someone discovers our podcast in 2020, they would find interest in listening to a lot of the back catalog. While there are some episodes that become dated quickly (Event, or launch specific episodes) even these might have elements or stories within them that resonate years later.
what questions do we ask?
Note to execute this well you need to do research on the guest (stalk them on twitter, blogs, recent press releases, LinkedIn) and try to get some questions that people in their field of experience would want to know. DO NOT ASK THE GUEST TO WRITE THE QUESTIONS. It comes off as disrespectful, (You don’t care enough to learn enough to ask an educated question). It is ok to ask if there are any recent announcements of themes they might want to cover, but do not make the guest do all the work here.
Critical elements of a good question are not jus what you ask, but what you do not ask.
Avoid leading questions
“Chad, it looks like Customers really like VCF because it provides enterprise reliability, can you explain why this is the most important reason to buy it? This is a terrrrrible question. If the question involves a run-on sentence, assumes you know more about the topic than the host, and narrows the response to “Yes, Mr host, you sure are right and smart” you are “doing it wrong!” . Instead of a less controlled question like “What are some common customer conversations you are having about VCF?” Sometimes you need to channel your inner Larry King and ask your questions like you know nothing. Starting with a level set question, and then asking questions off of that question and going deeper is a better method to allow the guest to explain things, and bring your audience with you rather than jump to a conclusion. A podcast series that interviews the greatest interviewers of all time is worth a listen.
How
The Gear
Gear is partly a function of the environment you record in. A $100 Sure SM58 in a professional recording studio, but in a small office may pick up sound bouncing off the hard walls. I’ve had the fortune of living near firehouses. Oddly enough “Podcasting booths or rooms” in some office buildings or conferences often have some of the worst aquistics ever created (Small rooms with hard glass surfaces are terrible for bouncing audio). Look for a blog series on “good/better best” gear for audio.
For now I’ll start with what not to use as it’s likely easier.
USB condenser microphones – The most popular example of these microphones are the Blue Yeti/snowball etc. Condensers are popular in studios (they can pull a lot of sounds in). The challenge with using these for office or home recording is you tend to end up “recording the room” (bounce off walls) and these microphones are aggressive at picking up background noise (air conditioning, fans, etc are easily picked up). You can do a lot worse than these (and we’ll get to this in a minute), but for serious audio recording in a less than functional environment be prepared to put some sound dampening on the walls, carpet in the room and turn off the air conditioning and fan. A downside of some of these USB mics is they often will not work with regular accessories (amplifiers, mixers, arms, highly custom-sized foam design) so you end up with a proprietary ecosystem around them.
Anything with a phone number – The public phone system tends to drop the quality of everything down to a common codec, G.711. This codec from 1972 is a “narrowband” codec and is (along with a host of other things) part of the reason why business travel exists. People don’t listen to podcasts by dialing into a voicemail, and you should want your podcast to sound better than their voicemail.
What I use?
I’m a fan of XLR based microphones. They make any investment in the Eco-system reusable later.
Microphone – Heil PR40. It’s dynamic and center-fire (Meaning it only records in a narrow angle) and that’s actually good for me. I don’t have a professional studio, the nursery is one room over, and fire trucks and barking dogs come past my office all the time. Note: this is an XLR microphone so I’ll need something to convert it to a digital signal. Pete also uses the same microphone, and that helps us get a similar sound after we match volume levels at the start of the podcast.
Input/Digitizer – For now I primarily use a Blue Icicle that is directly connected (no XLR cable used). I had some issues with the XLR cable built into my cheap arm mount and found that this avoided the need to get anything ti amplify the signal as it immediately goes from the microphone to being a digital signal. I’m still figuring out cable management for the USB cable. I also own a Sure digitizer that costs twice as much, but it was way too easy to hit the gain knob. The Blue requires some torque to turn and this means once you get it set you can largely ignore it.
Other things To go with the mic– I have the Heil foam for the mic to cut popping noises, and the heil branded shock mount (It prevents noise from when I hit the table while recording). I have an arm that is screwed into my desk (Was something cheap). If you are going to have a long XLR run, a quiet mic that needs a pre-amp something to amplify the signal (CloudLifter) might not be a bad idea. There’s no need to buy a mixer/board unless you are going to be blending multiple inputs (I’m not a DJ!).
In Person
For the road – When traveling to conferences we use tabletop stands and a Zoom H6 recorder. While it can act as a stand-alone recorder we normally feed it into a Mac using a USB cable into Audio Hijack and run some low pass filters and other effects. It offers support for 4 XLR inputs as well as individual gain control, can act as a handheld condenser with an attached microphone. Other software like Loopback can be handy for sending sound from a soundboard into another output.
Remote recording
Over the years we’ve tried a couple different bits of software. We started with:
Skype – which worked for a bit, but quality problems have gotten worse as Microsoft has slowly ruined it.
Skype for business – (an unmitigated disaster given our implementation uses narrowband codecs for remote employees when you have more than 2 people on a call).
Zoom.us – We settled on Zoom. It has a few interesting recording capabilities, like the ability to record every channel independently, and allow users to record locally. If you have network quality concerns this can help offset this allowing Pete in editing the podcast to delete parts when I was speaking over someone, or assemble local audio from a guest who was cutting in and out. This shouldn’t be needed often but it’s buried in the zoom web settings.
Editing –
We are doing it live! – Bill R
While it may seem easier to just record an hour and a half of audio and dump it to sound cloud, this is not what most people want to listen to. Part of the benefit to a podcast is not a live call is it allows you to leave some (or a lot) of an episode on the cutting room floor. Things that you can cut out:
- Mid program housekeeping discussions (Clarifying that we can introduce or avoid a given topic with the guest) or where you discuss the next segment
- Deleting things where you accidentally leaked NDA content.
- Letting someone try to respond to something again (however, if you obsess on perfection and require 10 takes to get something right Podcasts may be the wrong medium).
- Guests, off-color humor that you’d rather your VP not listen to while making pancakes with their kids.
- Long awkward pauses. We like to stress to guests if they want to sit and think for 10 seconds before responding “that’s fine”. Allowing awkward pauses gives people time to provide awesome content. It doesn’t sound great though on the podcast so we can cut them out.
- When John (Me) rambles off-topic or tries to speak over someone on accident.
- When you might have a good side conversation that might be useful in another montage episode on a topic.
The vSpeaking method? We REALLY try to keep podcasts in a 25-35 minute runtime when possible. Why this length? This is about the average commute time for a lot of our listeners (or time driving between customers for partners and customers). We might split a conversation up. We tend to block 1 hour for recording, use 5-10 minutes for housekeeping and setup, and record 40-50 minutes of content that is then edited down.
At Conferences like VMworld and events, we will often grab shorter 5-15 minute interviews. We will then stitch a collection of these into a longer episode using a windowing effect (we record an intro and outro for each segment). These “vignettes” might even be recorded as a small part of a larger episode. Episode 152 is an example of this format where we combined an interview with pat along with pieces of an interview with Brian Madden that will make up a future episode. This started out as a way for Pete and me to meet our goal of an episode every two weeks, by adapting the “Clip Show” method from television. These days this method is more about building an episode around a topic and provide more opinions and voices.
When
It’s worth noting that consistency is king in podcasting and publishing in general. If a podcast happens yearly, and is a 5-minute podcast, or is daily and is 3 hours long it will likely fail to grab a consistent listener base for a number of reasons. at least twice a month seems to be the minimum level of effort required for the length we run (25-45 minutes). Shorter podcasts tend to require much more frequent cadence to maintain listeners.
Length
It’s worth noting that consistency is king in podcasting and publishing in general. If a podcast happens yearly, and is a 5-minute podcast, or is daily and is 3 hours long it will likely fail to grab a consistent listener base for several reasons. at least twice a month seems to be the minimum level of effort required for the length we run (25-45 minutes). Shorter podcasts (8-10 minutes) tend to require more frequent cadence to maintain listeners.
A longer podcast allows some introduction banter, a longer intro song/music and a little more personality of the people speaking to come out. A short podcast (5-10 minutes) might work well for fitting into someone’s morning shower/shave/tooth brushing routine, but you’ll need to cut it down to more “just the facts”.
The VSpeaking Method: While there is some variety in the show length 25-35 minutes tends to be the target run time. This aligns well against the average, one-way commute time is 26.1 minutes, a 1 hour workout being able to fit two episodes.
Cadence
If you can’t commit to bi-monthly (24 episodes in a year) it may not be worth the investment. It’s hard to stay top of mind for listeners. Also consistent cadence can help. If you do weekly, then skip 2 quarters, then come back weekly it’s hard to remain part of the listeners “usual routine” where they listen to your podcast and make time for it. Assuming quality doesn’t suffer the more frequent, the better your subscriber numbers will look.
The VSpeaking Method: We started bi-monthly then shifted to bi-weekly then recently we have shifted to a “mostly-weekly” cadence.
Where
Where do you post it? Ideally, you want your podcast in every major podcast platform. You want the apple podcast app, Android play store, and Spotify. You will want a web player that allows people to play it from a browser, and you will want a website to host show notes, speaker notes, and other information.
Internal only podcast, or password protected – Call me cynical, but I don’t have faith in internal podcasts.
- There’s too much friction vs. using the existing apps that people use on their devices.
- It’s predicated on the myth that anything you post internal doesn’t easily leak out to competitors. Lets be honest, your secret competitive strategy if it’s any good will be published on TheRegister years before it ships or in the hands of your competitors before the ink dries. This might work for short form content that the embargo on will quickly be released.
The vSpeaking method: We host vSpeakingpodcast.com using Zencast.fm which provides hosting, and post-episode blogs on Virtual Blocks. We briefly flirted with an internal only podcast using socialcast as a distribution method (Sadly killed) or Podbean but for the quality and time commitment we make, we couldn’t justify it.
Conclusion
You need a few things to maintain a tech podcast.
- The drive to keep doing it. It has to be something you actually enjoy doing otherwise committing to blocking the time and doing the pre-work to get guests etc will result in it falling apart a month in.
- The right skills/talents. Pete is a fantastic showrunner, the host who keeps things moving, and editor.
- A genuine technical curiosity for the topics you will cover.
Help/SOS – Podcast Emergency you say?
if you’ve reached this section and you are trying to start a quality podcast please stop reading. If you are here because your boss came to you and said “we need you to start a podcast” keep reading. if you just discovered that your MBO/KPI for your quarterly bonus is tied to starting a podcast this section of the guide is exclusively for you. You don’t have any experience with any of this, and reading the above section has you convinced there is no way to be successful and it is too late to change this objective. It’s true, there isn’t really a market for un-edited poorly recorded 8 episode podcasts run by product marketing on “why you should buy our cloud product!” but that isn’t going to stop you from getting paid! Don’t stress, you will still be able to get your bonus if you follow the following guide.
Guests – Don’t try to get busy, highly in-demand guests. This might draw attention to the episode and highlight that this was just something slapped together to get a bonus.
KPI/MBO – Make sure the MBO/KPI didn’t include download statistics. Make sure to choose a platform that doesn’t provide this as part of it’s “free hosting” so you can blame that. In the event, you have some minimum downloads required just hire Mechanical Turk to get people to send you a screenshot of their phone saying “subscribed and downloaded”.
Quality Content? That will take too long. Just write out the ‘top 10 reasons you should buy our product’. Find the sales/marketing PowerPoint and feel free to just read the speaker notes (or slides, as we know speaker notes are for losers, and slides should have 100 words per slide). This is a great opportunity to reuse other stale content. For bonus points re-use content from someone who asked you to create a podcast so you can blame them if they don’t think the content is good!
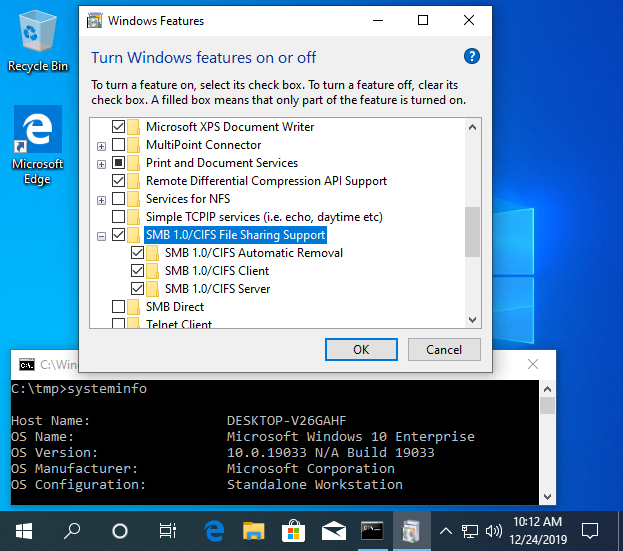
Gear? Use the official corporate standard for interoffice phone calls, especially if it’s quality is terrible. This will reduce the desire of whoever is reviewing this to give you your bonus to listen long enough to realize there is no real content. Skype4Buisness, Webex dial-in bridges
Editing? Leave 20-30 minutes of dead air on the end of the episodes to make them look longer. Especially if you are hiding the low-quality effort after the first episode as this will prevent it auto-playing the next episode.
Platform and marketing? – Consider posting this as MP3 on an internal-only sales education portal. Avoiding hosting it in the outside world will help avoid scrutiny. Make sure the metadata tags are not tracked well, and the only link to it is a weekly newsletter where it’s placed at the bottom.
What if I want to my product marketed by a Podcast and do not want to bother with all this?
This is a bit easier than the above steps. Simply reach out to some podcasts that have existing followings in your space, and see if you can get guests that will represent your product to that community. Sometimes this will cost money, sometimes this will not. Note: the vSpeakingpodcast does not do pay for play, but we don’t judge others in the industry who do as long as it is responsibly and legally disclosed.
There are also experienced people in the industry that you can just outright hire JMT being a good one right now.
Alternatively, if you want to produce a short video series, Video (A youtube playlist) is honestly a more popular format that is likely more conducive to what you are trying to accomplish.